What’s Defending Your Network?
Firewalls enforce rules. Antivirus protect computers. Neither can explain internal network activity, provide historical network evidence, or enforce segmentation. That's cybersecurity risk. Netabin's Managed SympleCyber Operations can reduce unmanaged cybersecurity risk.
Learn More About Netabin CybersecurityDoes Unmanaged Cybersecurity Risk Leave You Vulnerable?
“Would we know if ransomware was already inside our network?"
Ransomware can be in your systems for weeks before encryption detonation occurs.
Reduce risk with:
“We need to demonstrate compliance or oversight.”
State, federal, or internal requirements often demand visibility, documentation, and repeatable process.
Reduce risk with:
“Are guest and employee Wi-Fi devices exposing our business network?”
Guest devices, personal laptops, phones, and IoT systems often share the same network as business systems. Without proper separation and enforcement, Wi-Fi becomes an untrusted entry point.
Reduce risk with:
“Would we even know if someone was inside our network right now?”
Network and computer attacks can be silent. They can infest your LAN and go undetected.
Reduce risk with:
Netabin's Managed SympleCyber Operations Mitigate Risk
Our Managed SympleCyber Operations is the operational service model delivered by Netabin Cybersecurity.
The model provides continuous administration, monitoring, and evidence preservation through the SympleCyber (SC) control tool suite.
Each operational service is centered around a specific SympleCyber control tool: SC/IDS, SC/Firewall, and SC/Repository.
Detection, Protection, and Governance — Working Together
Managed
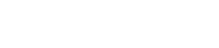
SC/IDS
Operations
Operates and administers:
- SC/IDS Control Tool
Primary Functions
- Managed Intrusion Detection System
- Security event collection and analysis
- Alert validation and investigation
- Digital forensic evidence retention
- Operational visibility reporting
Purpose
- Provide continuous detection visibility and documented evidence of network security activity.
- Detection findings inform enforcement actions and governance decisions within the SympleCyber control platform.
Managed
SC/Firewall
Operations
Operates and administers:
- SC/Firewall Control Tool
Primary Functions
- Firewall policy management
- Network traffic control and segmentation
- Configuration validation
- Security rule review and adjustment
- Traffic monitoring and logging
Purpose
- Enforce network boundary protection and maintain accountable firewall operations.
- Enforcement actions are traceable to governance decisions and validated through detection visibility.
Managed
SC/Repository
Operations
Operates and administers:
- SC/Repository Control Tool
Primary Functions
- NIST CSF governance activation
- Policy and standards management
- Evidence record preservation
- Governance decision documentation
- Aligns with SC/IDS & SC/Firewall
Purpose
- Establish an authoritative governance system of record that preserves security decisions, control alignment, and defensible evidence over time.
- Governance decisions guide detection priorities and enforcement policies across the SympleCyber control platform.
More Network Cybersecurity Risk Problems?
“We don’t know what’s actually happening on our network.”
Internet & internal activity, unusual behavior, and suspicious patterns often go unseen or lack context.
Reduce risk with:
“We need evidence for audits, insurance, or leadership.”
Without historical data and structured reporting, it’s difficult to demonstrate due diligence.
Reduce risk with:
“We see alerts—but don’t know if anything was actually blocked.”
Detection without enforcement confirmation creates uncertainty and unnecessary alarm.
Reduce risk with:
“Are our security cameras quietly exposed to the Internet?”
Computing devices are made all over the world. Some have "phone home" features that should not be allowed.
Reduce risk with:
New To Network Cybersecurity Defenses?
Start With Managed SC/IDS Operations
Firewalls and antivirus protect devices, but they don’t reveal what’s happening inside your network. SC/IDS provides continuous visibility into internal activity, identifying patterns such as:
Select One Of The Following Managed SympleCyber Operations To Learn More
Managed
SC/IDS
Operations
Continuous intrusion detection and alerting with structured review and reporting. Gain visibility into real network activity.
Learn MoreManaged
SC/Firewall
Operations
Active management of firewall rules and network access. Control LAN ingress, egress, and subnet security.
Learn MoreManaged
SC/Repository
Operations
Document, measure, and demonstrate your security posture. Structured policy and compliance management.
Learn More